
I went to Hamido Seafood last night for a friend’s birthday, an Egyptian fish restaurant in Astoria. You pick your fish, and they fry it up for you while you wait. So good. 🐟

I went to Hamido Seafood last night for a friend’s birthday, an Egyptian fish restaurant in Astoria. You pick your fish, and they fry it up for you while you wait. So good. 🐟
I started getting into The Dandy Warhols. The name really annoys me, but …The Dandy Warhols Come Down is great. 🎵
Andrew Sacher wrote a beautiful elegy for Brian Wilson on Brooklyn Vegan. RIP. 🎵
Brian resonates so much with indie/alternative/underground musicians because, no matter how famous The Beach Boys are, being a Brian Wilson fan means you’re in on one of the most profound secrets in all of pop music history.
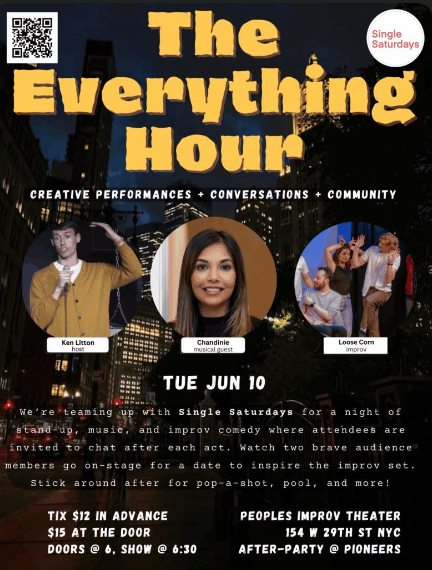
Had a great improv show with Loose Corn at The Everything Hour. Fun set, great audience. Thanks to Rachel and Remy for being our brave speed daters! 🎭
Just saw a dude walking down the street while eating a full plate of plain rice with a fork. Unglued.
Correction: five days ago, I got French metal band Animalize confused with their album title. The band name is Animalize, and the album is called Verminator, not the other way around.
This brought to you by the department of corrections no one complained about.
Oof, I’m late, but happy pride. 🏳️🌈🏳️⚧️
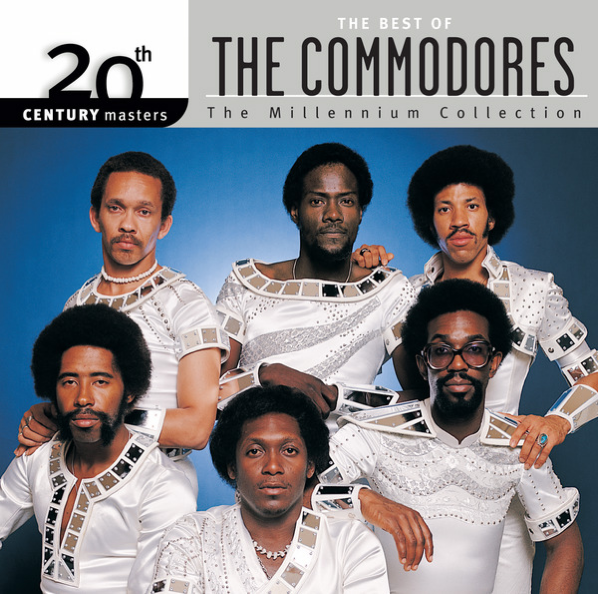
Everyone needs to reckon with how badass The Commodores looked.
There’s a guy selling pop up el pastor tacos a block from my apartment. Let’s go. 🌮
The 31st Ave open street is really cooking. You can tell because I’m doing the disco.

Day six of the micro.blog photo challenge on “contrast”. I think I nailed it. 📷

“Debutants and schoolboys.” This quote brought to you by a note I jotted down and forgot the entire context behind.
Great article on green dreamer kaméa about the importance of slowness in activism.
“Slowing down is not a function of speed. It’s not, ‘let’s take a break’, ‘let’s go on vacation’, ‘let’s leave it all behind.’ It’s none of that. Slowing down is a function of deepening awareness, noticing the others in the room.
I started listening to the article on 1.5x, then was like, “what am I doing?”
A little on the nose, but here’s my reflection for day 5 of the micro.blog photo challenge. 📷

I got a spider bite on my pointer finger last night. I’d point out that I don’t like spider bites, but that would be pointless. 🏴☠️
If this isn’t a big ‘ol nostalgia pile, I don’t know what is. Day 4 photo challenge. 📷

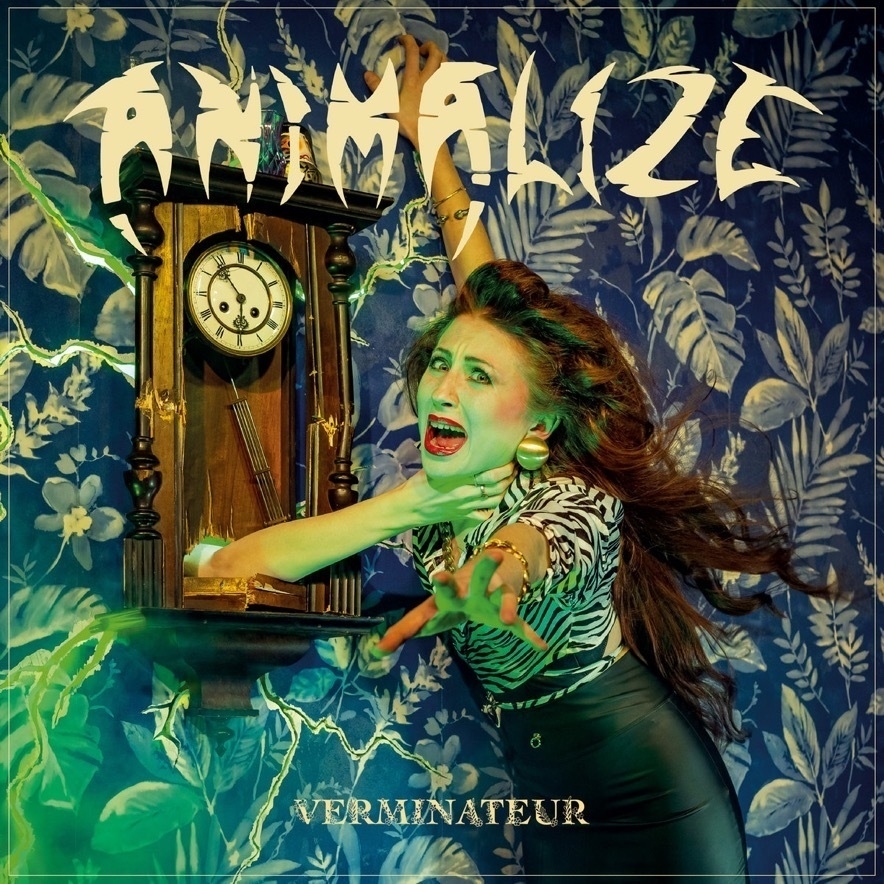
Been grooving to Animalize’s new album Verminator. They’re like if ‘80 glam and thrash metal got in a car crash in France. 🎵
Day 3 photo challenge. Shadow of the laundry chair. 📷

I snagged Head Of The Love Club, an EP by up and coming British pop singer Gretel Hänlyn, on the strength of Drive. Nothing else on the record comes close to that one for me, but there’s a lot of promise. She’s one to keep an eye on. 🎵
You know what I think? Me neither.
WTF with Marc Maron is ending. I’ve been listening since 2013, when I heard a clip of the Michael Keaton episode on WNYC while driving around Brooklyn. What a run. 🎙️
I’m convinced the primary motivation for the widespread AI push is for bosses to suppress wages and eliminate jobs. 💽
While in Penn State a few weekends ago, I got to have shoofly pie. You know what? Pretty damn good. 🥧

Spotlight (pun unfortunately intended) on an everyday industrial curve; who hasn’t benefited from the humble street lamp? 📸
I bought electronic music pioneer Susan Ciani’s 1982 album Seven Waves. Truly staggering atmospheric work. 🎵